Could a device on a home network be impersonating another trusted machine without any visible warning? That question sits at the heart of IP address spoofing, and the answer is a definitive yes. Understanding how to prevent IP address spoofing is no longer a concern reserved for enterprise IT departments; residential networks, home offices, and smart-home ecosystems face the same underlying vulnerabilities. This guide covers the full attack lifecycle — from packet fabrication through detection and remediation — drawing on the same principles explored in the site's broader network security guides.

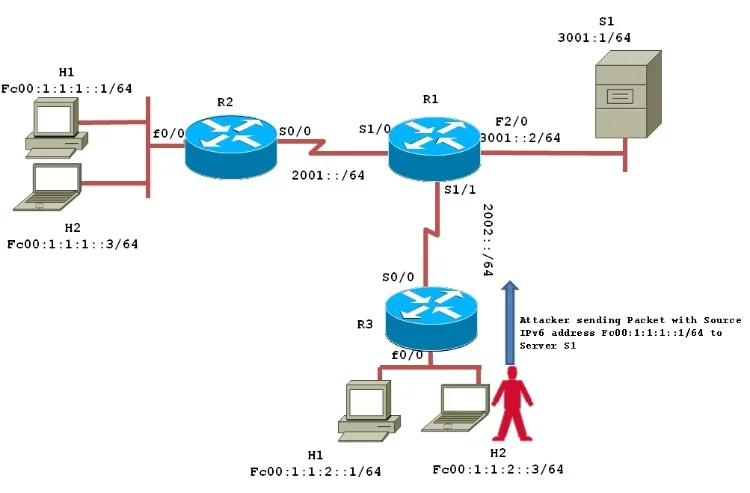
IP address spoofing occurs when a malicious actor crafts IP packets with a falsified source address, causing target systems and intermediary devices to treat the traffic as originating from a legitimate, trusted host. The technique exploits the foundational design of the TCP/IP protocol suite, which was engineered for reliability rather than source authentication. Because routers historically forwarded packets based on destination addresses alone, fabricated source fields passed unchecked across large portions of the global internet.
The consequences range from session hijacking and man-in-the-middle interception to amplified denial-of-service floods that can overwhelm residential gateways and small-business firewalls alike. Recognizing the architecture that enables spoofing is the prerequisite for every countermeasure discussed below.
Contents
What IP Address Spoofing Does to a Network
Packet Fabrication at the IP Layer
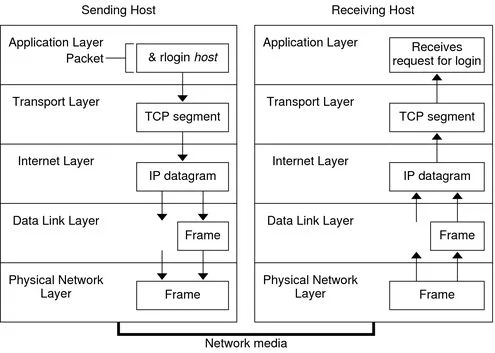
Every IP packet carries a source address field in its header — a value the sending host populates and the network largely trusts without independent verification. An attacker with raw-socket access writes any address into that field, redirecting responses, misdirecting forensic blame, or impersonating a trusted peer in a multi-party protocol exchange. The Wikipedia article on IP address spoofing provides a useful technical overview of the protocol-level mechanics for readers seeking the theoretical foundation in detail.
Connectionless protocols such as UDP are the primary vehicle for spoofed traffic, as they require no three-way handshake to establish a session. TCP-based spoofing is significantly harder to execute due to sequence number prediction requirements, yet it remains viable in specific network topologies where the attacker occupies an on-path position and can observe return traffic.
How Spoofed Packets Traverse Routers
Legacy network infrastructure treats the source address field as informational rather than authoritative. Without ingress filtering, border routers accept packets whose source addresses belong to entirely foreign address spaces, forwarding them toward declared destinations without challenge. This architectural gap is the foundation upon which every spoofing-based attack is constructed, and it explains why perimeter filtering remains the single most impactful defensive measure available to network operators of any scale.
Security tip: Enable ingress filtering on every upstream-facing interface — packets arriving on external interfaces bearing RFC 1918 internal source addresses should be dropped at the border router before they reach the forwarding path.
Common Attack Vectors That Exploit IP Spoofing
DDoS Amplification Attacks
Reflection and amplification attacks represent the most volumetrically destructive application of IP spoofing. An attacker sends small query packets — bearing the victim's IP address as the falsified source — to thousands of open resolvers or misconfigured services. Those services, believing the victim sent the original request, reply with responses many times larger in size, directing a concentrated flood of legitimate-looking traffic at the intended target.
- DNS amplification: query-to-response ratios reaching 70:1 from open recursive resolvers
- NTP monlist: amplification factors exceeding 550:1 in unpatched server implementations
- Memcached UDP: the highest documented factor on record, exceeding 50,000:1
- SSDP via UPnP: ratios between 30:1 and 50:1 from exposed consumer home devices
Residential internet connections are rarely the primary target in volumetric campaigns, yet smart-home devices with exposed UDP services can be conscripted as unwitting reflectors, making the home network complicit in attacks directed at external infrastructure.
Man-in-the-Middle and Session Hijacking
On-path attackers who can intercept and inject traffic use IP spoofing to assume the identity of one participant in an established session. Blind spoofing attacks — where the attacker cannot observe return traffic — depend on sequence number prediction, while true on-path attacks permit full session takeover once the authentic endpoint is suppressed or silenced. Just as understanding adversary behavior underpins physical security — a principle examined in the guide on how burglars think and what methods they use — understanding network attacker methodology is equally foundational to effective digital defense.
Notable Real-World Spoofing Incidents
Amplification Campaigns Targeting Infrastructure
The February 2018 GitHub DDoS attack reached a sustained throughput of 1.35 Tbps by exploiting Memcached servers with UDP port 11211 publicly exposed. Spoofed packets directed at approximately 50,000 misconfigured systems generated reflected traffic that briefly overwhelmed GitHub's network edge before upstream mitigation services rerouted the load. The incident remains the most precisely documented spoofing-based amplification event on public record and directly accelerated ISP adoption of BCP38 filtering requirements for subscriber-facing interfaces.
Smaller-scale amplification events occur daily against residential ISPs, targeting home routers that expose DNS resolvers or UPnP endpoints to the internet without restriction. Firmware updates that disable unnecessary public-facing services directly reduce a device's utility as a reflector node.
Spoofing in Targeted Intrusion Operations
State-sponsored operators routinely incorporate IP spoofing into multi-stage intrusion chains to complicate forensic attribution after the fact. By routing initial reconnaissance through spoofed source addresses — or by using spoofing to disrupt logging systems during the exploitation phase — operators introduce deliberate ambiguity into network telemetry records. The same predictive analysis techniques applied in crime forecasting to prevent physical burglaries find direct analogs in anomaly-based network intrusion detection, where deviations from established baseline traffic patterns serve as the primary signal for identifying spoofed packet floods before they reach saturation thresholds.
Spoofing vs. Related Network Threats
IP address spoofing is frequently conflated with adjacent techniques that share surface characteristics but differ meaningfully in mechanism, target layer, and required countermeasure. The table below clarifies the distinctions that network administrators and security-conscious home users need when selecting and deploying defensive tooling.
| Threat | OSI Layer | Spoofed Element | Primary Goal | Key Countermeasure |
|---|---|---|---|---|
| IP Spoofing | Network (L3) | Source IP address | Amplification, evasion, impersonation | BCP38 ingress/egress filtering, uRPF |
| ARP Spoofing | Data Link (L2) | MAC-to-IP mapping | On-path interception on local segment | Dynamic ARP inspection, static ARP entries |
| DNS Spoofing | Application (L7) | Domain resolution records | Redirect users to malicious hosts | DNSSEC, DNS-over-HTTPS |
| Email Spoofing | Application (L7) | From/Reply-To headers | Phishing, social engineering | SPF, DKIM, DMARC enforcement |
| MAC Spoofing | Data Link (L2) | Hardware address | Bypass MAC-based access controls | 802.1X port-based authentication |
How to Prevent IP Address Spoofing: Core Defensive Techniques

Ingress and Egress Filtering
BCP38 (RFC 2827) defines the canonical approach to network ingress filtering at the ISP and enterprise perimeter. Packets arriving on an interface should carry source addresses topologically reachable via that same interface; packets that fail this sanity check are dropped before they enter the forwarding path. Egress filtering applies the same logic in reverse — packets leaving the network with source addresses outside the organization's assigned prefixes are blocked at the outbound edge before they reach the upstream provider.
- Configure access control lists on all border router interfaces facing the public internet
- Block RFC 1918 private-range source addresses arriving on any external-facing interface
- Block loopback addresses (127.0.0.0/8) on all external interfaces without exception
- Block current Bogon prefixes as defined by the IANA Special-Purpose Address Registry
- Enforce egress ACLs to prevent internally originated spoofed traffic from exiting the network
Unicast Reverse Path Forwarding (uRPF)
uRPF automates BCP38 enforcement at the router level by verifying that the source address of an incoming packet is reachable via the interface on which it arrived. Strict mode drops any packet whose source does not match a route pointing back through that same interface; loose mode drops packets whose source addresses have no valid route in the routing table at all. Strict uRPF is the more effective configuration on single-homed interfaces, while loose mode accommodates asymmetric routing in multi-homed or complex enterprise environments.
Encrypted Transport and Cryptographic Authentication
IPsec in transport or tunnel mode cryptographically binds each packet to an authenticated identity, making source-address forgery detectable rather than silent. TLS mutual authentication achieves the same outcome at the session layer for web-based services and API endpoints. Home offices connecting via corporate VPN benefit from these protections by default, provided the VPN gateway enforces certificate-based authentication rather than relying exclusively on pre-shared keys, which offer no per-packet binding guarantees.
Ongoing Monitoring and Network Upkeep
Continuous Traffic Analysis
Passive monitoring of NetFlow or sFlow telemetry exposes asymmetric traffic patterns characteristic of spoofing-based attacks — notably the absence of reciprocal TCP handshake traffic for inbound connection attempts appearing in the log. Intrusion detection systems with spoofing-specific rule sets flag packets bearing internal source addresses arriving on external interfaces, a reliable indicator of either serious misconfiguration or an active spoofing campaign in progress.
- Review firewall deny logs weekly for RFC 1918 source addresses on external interfaces
- Configure threshold alerts for UDP amplification traffic patterns: DNS, NTP, and SSDP
- Audit router ACLs quarterly to ensure Bogon lists reflect current IANA address assignments
- Apply router and firewall firmware updates within the vendor's published patch window
Router and Firmware Hygiene
Consumer-grade routers shipped with UPnP enabled on WAN-facing interfaces represent a persistent reflector surface for amplification campaigns operating at scale. Disabling UPnP, closing unnecessary UDP services, and confirming that the ISP-provided device applies BCP38-compliant filtering at the subscriber edge are the minimum-viable hygiene steps for any network with internet-exposed devices. Firmware updates applied within the vendor's recommended window close documented amplification vectors before adversarial scanning infrastructure catalogs and exploits them systematically.
Frequently Asked Questions
What is IP address spoofing?
IP address spoofing is the practice of crafting network packets with a falsified source IP address in the IP header, causing receiving systems to misattribute the traffic's origin. Attackers use this technique to impersonate trusted hosts, evade access controls, or misdirect responses from amplifying services toward an intended victim target.
How does IP spoofing differ from using a VPN?
A VPN assigns a legitimate IP address from the provider's address pool and routes all traffic through an encrypted, authenticated tunnel — the traffic originates from a real, routable address that the provider controls. IP spoofing, by contrast, inserts a fabricated source address that the attacker does not own and cannot receive return traffic on, a fundamental structural distinction that separates privacy tools from attack techniques entirely.
Can a home router be protected against IP address spoofing?
Home routers with configurable ACL or firewall rule support can enforce BCP38-style ingress filtering, blocking inbound packets whose source addresses belong to the local network or private RFC 1918 ranges arriving on the WAN interface. Disabling UDP-based services exposed to the public internet — particularly UPnP and open DNS recursion — further reduces the device's utility as an unwitting amplifier in reflection attacks targeting external parties.
Is IP address spoofing illegal?
In most jurisdictions, IP address spoofing conducted with malicious intent — to facilitate unauthorized access, denial-of-service attacks, or fraud — constitutes a criminal offense under computer misuse and cybercrime statutes. Legitimate applications, such as network resilience testing within an authorized penetration testing engagement, are permissible provided that explicit written authorization clearly covers the scope, methods, and IP ranges involved in the assessment.
Final Thoughts
IP address spoofing exploits architectural assumptions baked into the internet's foundational protocols, and no single tool eliminates the threat entirely — but a layered posture combining BCP38 ingress filtering, uRPF enforcement, cryptographic session authentication, and regular firmware hygiene reduces the attack surface to a manageable level. Network administrators and home users alike should audit their perimeter rules against current Bogon lists, disable unnecessary UDP services on internet-facing devices, and ensure that any VPN or remote-access solution enforces certificate-based identity rather than shared secrets. Begin with the router's WAN interface today — a single correctly configured ACL can remove a device from the reflector pool entirely and meaningfully reduce risk for the broader network community.





About Robert Fox
Robert Fox spent ten years teaching self-defence in Miami before transitioning into home security consulting and writing — a background that gives him an unusually practical, threat-aware perspective on residential security. His experience spans physical security assessment, lock and alarm system evaluation, and the behavioral habits that make homes harder targets. At YourHomeSecurityWatch, he covers home security product reviews, background check and criminal records resources, and practical guides on protecting your property and family.
You can Get FREE Gifts. Furthermore, Free Items here. Disable Ad Blocker to receive them all.
Once done, hit anything below



