More than 10 billion RFID tags enter the global supply chain every year, and a fast-growing share of them end up controlling physical access — from hotel corridors to residential front doors. Understanding how RFID lock systems work is now a practical necessity for any informed home security decision, not merely a subject for engineers. Our team at YourHomeSecurityWatch has evaluated these systems across dozens of real installations, and one finding is consistent: the technology rewards those who understand it and creates exploitable gaps for those who don't. Our complete RFID locks guide covers the full product landscape in detail.
RFID stands for Radio-Frequency Identification. The concept traces back to World War II military identification transponders — a history documented in depth on Wikipedia — but the first modern RFID patent was filed in 1983. Consumer-grade residential lock hardware didn't reach mainstream retail until the early 2000s, and adoption has accelerated sharply since. Today's RFID door locks are compact, durable, and engineered to integrate with modern smart home platforms.

Our research across product categories and live installations has confirmed that most home users carry at least one major misconception about these systems — misconceptions that translate directly into security vulnerabilities or wasted spending. The sections below address the mechanics, the hardware, the honest trade-offs, and the practical decision framework that matters most for real-world home security.
Contents
- Common Misconceptions About RFID Lock Security
- How RFID Lock Systems Work in Practice
- The Hardware Behind Every RFID Door Lock
- Troubleshooting Common RFID Lock Problems
- Honest Pros and Cons of RFID Lock Systems
- RFID vs. Traditional Locks: A Side-by-Side Comparison
- When RFID Locks Are the Right Choice — and When They're Not
- Frequently Asked Questions
Common Misconceptions About RFID Lock Security

Our team regularly encounters the same cluster of misbeliefs when speaking with home users about RFID-based access control. Clearing these up before any purchase or installation prevents costly and dangerous mistakes.
The "Unhackable" Myth
Marketers occasionally imply that RFID locks are immune to compromise. That claim is flatly false. Determined attackers with off-the-shelf hardware can clone certain low-frequency (125 kHz) credentials in under ten seconds using equipment that costs less than $20. The security level of an RFID lock depends entirely on the encryption standard and frequency it uses — not on the mere fact that it uses RFID. High-frequency (13.56 MHz) locks running protocols like MIFARE DESFire EV2 or ICLASS SE with AES-128 encryption are dramatically harder to attack. Our recommendation is always to verify the encryption standard before committing to any system.
- 125 kHz (LF): easily cloned, no native encryption — found in many older budget residential locks
- 13.56 MHz (HF): supports mutual authentication and AES-128 encryption, the right choice for home security
- 860–960 MHz (UHF): long-range reads, designed for vehicle gates and warehouses — not appropriate for front doors

The "Too Complicated" Myth
The opposite misconception is equally common: that RFID systems require specialized IT knowledge to operate. Modern residential units are engineered for non-technical installation. Most systems involve mounting a reader unit, wiring it to a door strike or motorized bolt, and programming credentials through a simple app or keypad sequence. Our experience shows that most home users complete a basic single-door RFID installation in under two hours without professional assistance.
Pro tip: Always register at least two backup credentials (cards or fobs) before locking the system down — losing access to a properly secured RFID lock typically requires a full factory reset that wipes every registered entry.
How RFID Lock Systems Work in Practice
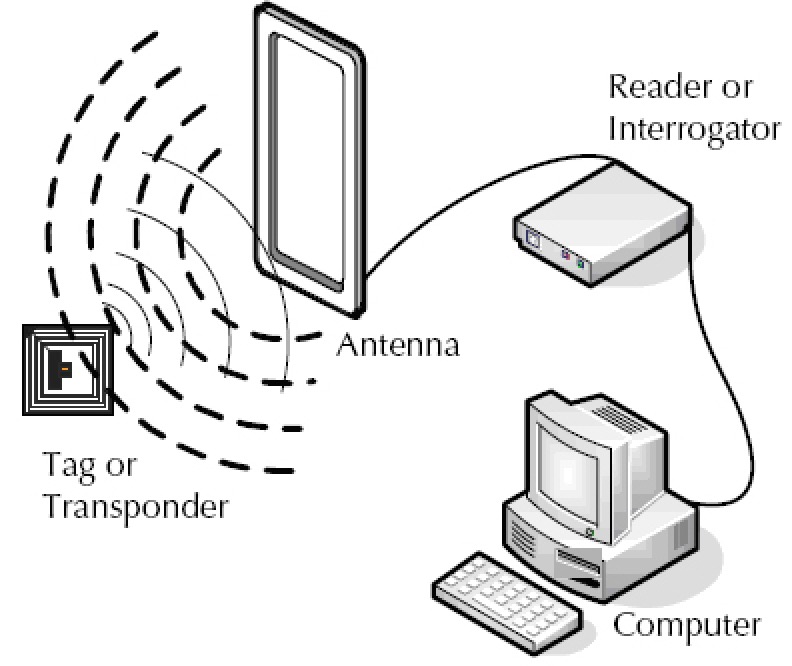
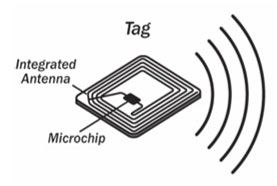
At its core, how RFID lock systems work comes down to a wireless exchange between two components: a credential (card, fob, or wristband) and a reader. No physical contact is required. The reader continuously broadcasts a low-power electromagnetic field; when a compatible credential enters that field, it draws energy from it and transmits a unique encrypted identifier back to the reader. The entire exchange takes milliseconds.
The Basic Authentication Sequence
Here is the full authentication cycle our team has documented across multiple system types and brands:
- Reader activates field — emits a continuous RF signal within a defined range, typically 1–10 cm for secure residential locks
- Credential enters field — the tag's embedded antenna coil picks up the electromagnetic energy and powers the internal chip
- Tag transmits UID — the chip sends its unique identifier, along with a cryptographic challenge response if the system supports mutual authentication
- Reader validates — the reader's onboard controller compares the received data against its stored authorized credential list
- Lock actuates — on a successful match, the controller signals the electric strike, magnetic lock, or motorized bolt to disengage
- Audit log written — networked systems record the credential ID, timestamp, and access point for later review

Frequency Ranges and What They Mean
The operating frequency shapes the security profile, read range, and compatibility of any RFID lock. Our team consistently advises home users to select 13.56 MHz systems over legacy 125 kHz options. The practical differences are significant and should drive every purchasing decision:
- 125 kHz: short read range (~10 cm), no encryption, widely cloneable — still found in older office access systems and certain budget residential locks sold online
- 13.56 MHz: supports AES-128 and mutual authentication protocols, the dominant standard in every major hotel brand and most quality residential RFID locks
- NFC (subset of 13.56 MHz): enables smartphone-based credential entry on compatible locks — the same chip family, just optimized for peer-to-peer communication
The Hardware Behind Every RFID Door Lock

Every RFID lock system — from a $150 residential deadbolt to a $5,000 enterprise access controller — consists of the same foundational hardware components. Understanding these pieces helps home users make smarter purchasing decisions and diagnose problems when they arise.
RFID Tags and Credentials
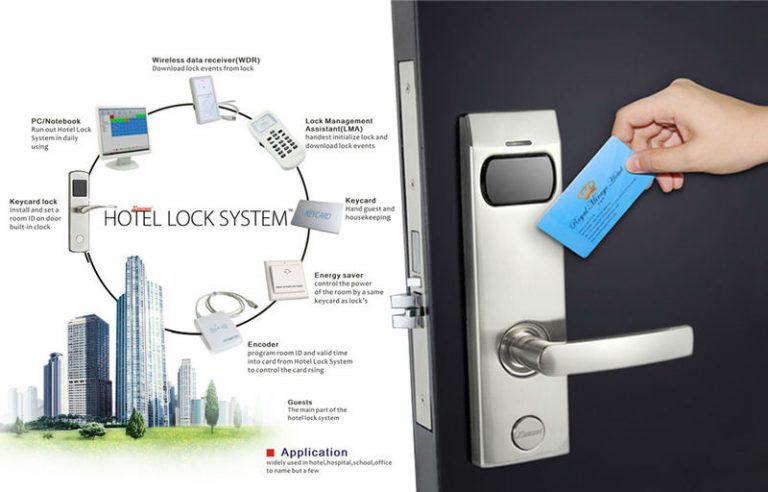
The credential is what the end user carries or presents. RFID credentials come in several physical forms, each suited to different environments:
- Key fobs: compact, keychain-friendly, highly durable — the most common residential credential by a wide margin
- Smart cards: credit-card-sized, often dual-frequency for compatibility across multiple reader types in shared access environments
- Wristbands: common in hotel and gym settings, with an embedded chip sealed inside silicone or PVC
- Stickers: thin NFC stickers that can be affixed to an existing item — wallet, phone case, or keychain — for discreet credential embedding

All of these credentials are passive — they carry no battery. Power comes entirely from the reader's electromagnetic field during the brief authentication moment. This is why RFID credentials last for years or even decades without any maintenance or charging.
Readers and Controllers
The reader is the active component mounted at the door. It handles both the RF transmission and the credential validation logic. In a standalone residential lock, the reader and controller are integrated into a single weatherproof unit. In larger access control systems, they are separate — a reader mounted flush on the door face communicates with a central controller panel managing multiple entry points simultaneously.
- Standalone locks: all-in-one, battery-powered, best for single-door residential use — the simplest upgrade path
- Networked systems: controller connects via Wiegand protocol, RS-485, or TCP/IP — required for multi-door deployments and enterprise access management
- Electric strike vs. magnetic lock: electric strikes release the door frame mechanism; magnetic locks hold the door face with an electromagnet — each carries different fail-safe implications during a power outage

For home security applications, our team consistently recommends pairing an RFID lock with a mechanical secondary layer. Understanding how a deadbolt works mechanically clarifies why the two technologies complement each other well — RFID handles keyless credential management, the deadbolt provides a physical fallback that remains functional without power.
Troubleshooting Common RFID Lock Problems

Even well-maintained RFID systems develop issues over time. Our team has documented the most frequently reported problems from home users, along with the most effective diagnostic steps and fixes.
Read Failures and Dead Zones
Intermittent read failures — where a credential doesn't register on the first presentation — are the most common complaint. The causes are almost always structural or environmental:
- Metal interference: steel door frames and metal-core doors dampen the RF field significantly. Anti-metal booster tags or plastic spacer plates between the reader and the metal surface resolve most cases.
- Reader orientation: the credential must be presented flat and parallel to the reader face. An angled presentation places the antenna outside the optimal read zone.
- Low battery: most standalone RFID locks run on AA or CR123A cells. Field strength drops noticeably below 20% charge — most units produce an audible low-battery alert before failure.
- Firmware version: some manufacturers release firmware updates that adjust field sensitivity and authentication timing. Checking the manufacturer's support portal is always worth doing before replacing hardware.
Credential and Card Issues
Cards and fobs fail more often than the lock hardware itself. Most credential failures fall into three categories our team sees repeatedly:
- Physical damage: a bent or cracked card loses antenna integrity — a hairline fracture across the internal coil renders the card completely unresponsive even if visually intact
- Inadvertent deletion: certain lock models erase all stored credentials when the master card is presented twice in quick sequence — always store the master card separately from daily-use credentials
- Compatibility mismatch: budget locks sometimes accept only a narrow range of credential protocols. A 13.56 MHz card will not authenticate on a reader tuned exclusively to 125 kHz, even if both look identical
Warning: The widespread belief that RFID cards get "demagnetized" by proximity to magnets is a myth — RFID chips are unaffected by magnetic fields. Only cards with a magnetic stripe are at risk, and that stripe has no role in RFID authentication.
Honest Pros and Cons of RFID Lock Systems

Balanced evaluation matters more than marketing language. Our team has tested enough RFID lock hardware across enough real installations to offer a straightforward assessment of where this technology genuinely excels and where it falls short.
Advantages Worth Knowing
- No mechanical key to lose or copy: misplaced credentials are deleted from the system in seconds with no locksmith required
- Instant access revocation: removing a contractor, ex-tenant, or former household member takes a few button presses, not a rekey appointment
- Audit trail capability: networked systems log every entry event with credential ID and timestamp — invaluable for rental properties and multi-occupant households
- Speed and reliability: tap-to-enter takes under half a second and works equally well in the dark, rain, or with gloved hands
- No mechanical keyway to pick, bump, or impression: the entire class of traditional lock picking attacks is eliminated at the hardware level
Limitations Home Users Should Understand
- Power dependency: electric strike and motorized bolt locks require continuous power — a power outage without battery backup can leave a door locked or unlocked depending on the fail-safe setting
- Credential cloning risk on legacy systems: unencrypted 125 kHz cards are cloneable with hardware available on major retail sites for under $20
- Higher upfront cost: a quality RFID lock system runs $150–$500 installed vs. $50–$150 for a Grade 1 deadbolt
- Servicing complexity: a residential locksmith experienced with mechanical hardware may have no familiarity with a given RFID system's controller firmware or credential management software
Our team also strongly recommends pairing any electronic lock upgrade with physical door hardening. Reviewing proven door hardening techniques is a practical next step — the door frame and strike plate are consistently the weakest point in a residential entry, regardless of how sophisticated the lock hardware is.
RFID vs. Traditional Locks: A Side-by-Side Comparison
When advising home users on lock selection, our team applies a consistent comparison framework across security, cost, and practical management. The table below reflects aggregated evaluation across dozens of products in each category.
| Attribute | RFID Lock System | Traditional Deadbolt | Mortise Lock |
|---|---|---|---|
| Pick/bump resistance | Excellent — no keyway | Moderate (Grade 1 is good) | Very good |
| Credential cloning risk | Low (13.56 MHz encrypted) / High (125 kHz) | None | None |
| Lost credential response | Instant digital revocation | Rekey or replace ($50–$150) | Rekey ($75–$200) |
| Power requirement | Battery or hardwired | None | None (fully mechanical) |
| Average cost installed | $200–$600 | $50–$150 | $200–$450 |
| Access audit trail | Yes (networked systems) | No | No |
| DIY installable | Yes (standalone models) | Yes | Rarely |
| Weather/outdoor rating | IP65 (quality units) | ANSI Grade 1 | Weather strip required |
Security Levels Compared
The security comparison is nuanced. A well-chosen RFID lock eliminates the entire class of traditional lock-picking and bump-key attacks. However, it introduces electronic attack surfaces — relay attacks, replay attacks, and credential cloning on under-encrypted systems. The most secure residential installations pair an encrypted HF RFID system with a Grade 1 mechanical deadbolt. Each layer addresses a different threat model, and understanding how mortise locks work puts the mechanical side of that equation in context for anyone considering a full door hardware upgrade.
Cost and Installation Reality
Cost comparisons depend heavily on scope. A single-door residential RFID lock from a reputable brand (Schlage, Assa Abloy, August) typically costs $150–$350 for hardware alone. Networked multi-door systems scale into the thousands. Traditional deadbolts remain the per-door cost winner. That said, the long-term credential management savings — no locksmith rekeying, no physical key duplication, no lockout callout fees — partially offset the premium for properties with regular access turnover.
When RFID Locks Are the Right Choice — and When They're Not

The technology is not universally appropriate. Our team applies a consistent decision framework when assessing whether RFID lock systems are the right fit for a given property, budget, and use case.
Ideal Use Cases
RFID excels in scenarios where credential management and access logging outweigh the cost premium:
- Rental properties with frequent tenant or short-term guest turnover — revoke and reissue access instantly without a locksmith
- Multi-person households where individual access schedules or restriction levels need ongoing management
- Home offices or outbuildings containing sensitive equipment that requires access-level separation from the main household
- Properties where service providers (housekeepers, dog walkers, contractors) need time-limited or time-scheduled access
- Secondary entry points like garages, mudrooms, or pool gates where physical key management is impractical and access logging is valuable
When Conventional Locks Still Win
There are genuine scenarios where traditional lock hardware is the more sensible choice. Our team does not recommend RFID systems as a universal upgrade:
- Single-occupant properties with stable access: a Grade 1 deadbolt provides excellent security at a fraction of the cost when credential management is irrelevant
- Locations without reliable power access or where battery replacement is impractical — an unpowered RFID lock becomes inaccessible
- Environments near heavy electromagnetic interference sources — certain industrial equipment and antenna arrays affect reader sensitivity
- Budget-constrained retrofits where door frame reinforcement and a quality mechanical lock deliver 80% of the security improvement at 20% of the cost
- Historically designated properties where surface-mount electronic hardware is either prohibited or visually incompatible with the architecture
For properties where the economics or use case don't support RFID, investing in quality mechanical lock hardware and reinforced door frame components remains one of the highest-value residential security improvements available.

Frequently Asked Questions
Can RFID lock credentials be duplicated without the owner's knowledge?
Yes — but only on systems using unencrypted 125 kHz credentials. An attacker with a compatible reader placed within a few centimeters can silently capture and clone such a card. Modern 13.56 MHz systems with mutual authentication prevent this entirely because the clone attempt fails the cryptographic challenge. Our team's consistent advice is to avoid any residential RFID lock that does not explicitly specify its encryption standard and frequency in the product documentation.
What happens to an RFID lock during a power outage?
The answer depends on the lock's fail-safe configuration. Battery-powered standalone locks continue operating on their internal cells regardless of mains power. Hardwired electric strike locks default to either fail-safe (unlocked during outage) or fail-secure (locked during outage) — the appropriate setting depends on fire egress requirements and local building codes. Our team recommends confirming the fail-mode setting before finalizing any hardwired installation, particularly on primary exit doors.
How many credentials can a typical residential RFID lock store?
Most quality standalone residential RFID locks store between 100 and 500 unique credentials, with higher-end networked systems supporting thousands. For single-family residential use, 100 entries is more than adequate. Our experience shows that most households actively use fewer than ten credentials at any given time — the rest are registered backups, temporary entries, or legacy credentials that should be purged regularly as a security hygiene practice.
Are RFID locks reliable for outdoor use?
Quality units rated IP65 or higher handle rain, dust, and temperature variation reliably. The reader face and credential interaction are not affected by moisture in IP65-rated systems. The more important consideration is battery performance in cold climates — lithium AA cells outperform alkaline below freezing temperatures and are our team's standard recommendation for any outdoor RFID installation in regions with winter temperatures below 0°C (32°F).
How does an RFID lock differ from a Bluetooth or Wi-Fi smart lock?
RFID locks authenticate via passive radio-frequency credentials — cards, fobs, or wristbands — with no smartphone or internet connection required. Bluetooth and Wi-Fi smart locks authenticate via smartphone apps and depend on the phone's battery, the app's connectivity, and in many cases a cloud server. RFID systems are more operationally independent and have no app dependency, which our team considers a significant reliability advantage for primary entry points. The two technologies are frequently combined in modern hybrid locks that support both credential types.

The lock on the door is only as strong as the knowledge behind the decision to install it — choosing the right RFID system, at the right frequency, with the right encryption, is what separates genuine security from expensive theater.





About Robert Fox
Robert Fox spent ten years teaching self-defence in Miami before transitioning into home security consulting and writing — a background that gives him an unusually practical, threat-aware perspective on residential security. His experience spans physical security assessment, lock and alarm system evaluation, and the behavioral habits that make homes harder targets. At YourHomeSecurityWatch, he covers home security product reviews, background check and criminal records resources, and practical guides on protecting your property and family.
You can Get FREE Gifts. Furthermore, Free Items here. Disable Ad Blocker to receive them all.
Once done, hit anything below



