Welcome to Your Home Security Watch
We provide local smart security installation & mantenance for the city of Santa Clara, California. Hit us on Social Media pages and here for more detail.
Alarms & Sensors
There's no way we can run a home security website and not talk, at length, about alarms and sensors.
In the modern world, meaning the past 50 or so years, electronic alarms and sensors have come on to the scene as a truly practical means of helping to protect your home or business from intruders.

Of course, in reality, alarms and sensors are not the same. They each perform different jobs, and function differently.
But, they are similar in that their purpose, generally, is to notify you when something occurs.
Alarms
For alarms, typically if there is a break in, an alarm will either sound loudly, or silently, notifying you one way or another that there is an intruder.
Or, for the purposes of some businesses, an alarm will sound if someone tries to steal something, as certain alarms can detect items leaving a store without being paid for.
Some of the brands we mention here on the site include: Vinker, SimpliSafe, Fortress, GE, among others.
Sensors
Sensors are different from alarms in that they are designed to sense a variety of things, such as detect motion, water, temperature, and so forth. Some sensors perform multiple functions and are considered multi-sensors.
These days, sensors are affordable and modern-looking, and you can pick them up almost anywhere. Some sensors, just to look at them, you have no idea what they do or are capable of!
Many sensors these days are smart, and can send notifications to your smart phone if there's anything to report.
Sensors often link to some sort of main hub in order to communicate with their owner.
Both alarms and sensors require strategy on your part to make the most of them, like anything else. Before buying an alarm or sensor, it's best to think, in advance, of what you will do with it.
Please browse our section here on alarms and sensors and gather the information you need to make an informed purchase!
Boat Security

Boat security is distinct from other types of security, because it involves a number of different considerations not present in other forms of security, the main distinguishing feature being that of the presence of water.
So, in some ways, it can be compared to home security or car security, in that there are required locks to prevent theft, and some thieves are looking to either break in, or steal your outboard motor, or even your fuel.
If someone does manage to steal your boat, by the time that thief is out on the water, this relies on different authorities to take care of things, rather than the police. Devices like tracking beacons may be utilized was well.
Sometimes the people who can help you the quickest are your fellow boaters in Boatwatch, so it’s good to be familiar with that organization if you already aren’t.
Overall, this section is filled with reviews of the best boat security gear you can get, and plenty of great tips as well. Leave us a comment as well, we’d love to hear from you!
Childproofing Your Home

But as any parent knows, kids sometimes can get into trouble doing the littlest things, and this is when actual childproofing of your home becomes necessary. As much as we want them to explore, the must explore in the safest of environments, or else risk injury.
With childproofing, this extends to everything from extension gates, to video monitors, to special window and door accessories that make it so your child can’t open the window and climb out. The list of childproofing products is extensive.
We also provide our readers with additional tips and tricks to make your home completely childproof, so do yourself a favour and check through this section for articles that we hope can help you a lot.
Leave us a comment and let us know your thoughts on childproofing as well!
Baby Gates
When it comes to childproofing your home, one of the main things you’ll be wanting is a baby gate.
If you have a baby in the house who can crawl, walk, toddle, run, or otherwise hurl themselves one way or another, it’s probably time for a baby gate.
The purpose of a baby gate gate is obvious – to keep them from going where they ought not go, ie. towards doors or stairs.
Babies, if you’ve ever had one or seen one in action, are quick. Super quick. Alarmingly fast, in some cases.
And so, when buying a baby gate, it needs to be high enough, strong enough, and flexible enough to prevent your child from getting past it, while also not injuring your child by being unusually hard or pointy.
Babies, being the relative height of the gate itself, often slam into these things full speed, and may even start sucking on the bars immediately.
So, you will want a gate that’s easy to clean, have some give to it (for impacts), portable, and doesn’t have any inherent flaws that would make it a hazard in any way to your child.
Another thing you’ll be wanting in a baby gate is something that looks good. Yes, ultimately baby gates are functional, but they can still get worn down and make your home look like the inside of a zoo, if they get dilapidated enough.
So the point would be to not spend a mint, but to get something that is aesthetically pleasing. Not just buy something that looks like it might belong in a baby prison!
That’s what we talk about in this section – baby gates – as well as other things to look out for, and we hope you find this information helpful!
Computer Security
In this section, we focus on computer security.
Historically, since the advent of computers, home security has been one thing, while computer security is another. There wouldn’t seem to be a correlation between how tough your deadbolt is and what a computer is doing.
And yet, these days, with smart home technology becoming more and more integrated into our homes, there is a need to take a closer look at computer security, because it is intertwined with home security in a very fundamental way.
In fact, computer security is just as important for us as home and business owners, not to mention our families, as any other kind of security right now.
Therefore, we must educate ourselves as much as we can on this topic, so that, for instance, our phones and home internets don’t get hacked and overtaken by nefarious people who are looking to do so.
And, whereas criminals of the past were a certain type of person, or stereotype, nowadays, a cyber-criminal is a whole different kind of criminal.
These criminals aren’t thugs, they’re computer nerds and tech savvy people who have the ambition to steal from you without having to knock your door down or climb through your window.
Things like our bank accounts, or our identities, or the control over our smart homes can be at stake when our security is compromised, and so here we offer articles on how to make things more secure in regards to our computers.
Topics we cover here involve identifying online security threats, preventing people from hacking into your smart home, best practices for being safe on the web, hacking, IP address spoofing, phishing, and even how to improve website security.
Leave a comment to share your thoughts with us as well.
VIPERTEK VTS-989 Heavy Duty Stun Gun Review
Stun guns are growing in popularity as a means of personal protection for many reasons. They are more affordable than … Read moreVIPERTEK VTS-989 Heavy Duty Stun Gun Review... [read more]
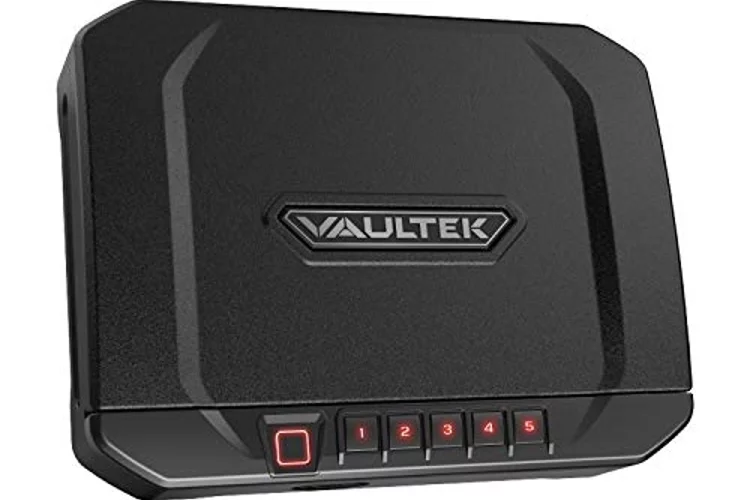
VAULTEK VT20i Biometric Handgun Safe Review
A handgun is meant to keep you safe, but it's also something you need to keep safe. There are many examples of why you need to keep your handgun in a safe. It could be that you have small children in the house... [read more]
ZOSI Security Camera Review
Zosi 1080P Hd 1920Tvl Hybrid 4-In-1 Tvi/Cvi/Ahd/960H Cvbs Cctv Surveillance Weatherproof Bullet Security Camera 42Pcs Infrared Leds, 120Ft Ir … Read moreZOSI Security Camera Review... [read more]
Winter Home Security Tips
Taking necessary precautions to increase the safety in and around your home is always a good idea, especially in winter.Generally, this period of the year is connected to higher burglary rates and home accident... [read more]
Wink Company Information
Launched in 2014, Wink is a software and hardware platform with a focus on smart home applications. As with many tech start ups these days, Wink began with a dream and some help from crowd-funding from their pa... [read more]
Who Invented The Burglar Alarm?
Who invented the burglar alarm? These devices are so common these days, that it’s difficult to imagine a time when there … Read moreWho Invented The Burglar Alarm?... [read more]
Which Schlage Locks Are Bump Proof / Bump Resistant?
Every homeowner shares at least one concern… keeping their home safe from the common criminal. Locks are more or less … Read moreWhich Schlage Locks Are Bump Proof / Bump Resistant?... [read more]
What’s The Difference Between Bump Proof And Pick Proof Locks
Homeowners of course want to feel that their homes are protected at all times against intruders. In the past, people … Read moreWhat’s The Difference Between Bump Proof And Pick Proof Locks... [read more]
What Makes a Deadbolt Lock Secure?
According to Department of Justice statistics, around 35% of home break-ins are committed by burglars who come right through the … Read moreWhat Makes a Deadbolt Lock Secure?... [read more]
How Are Gun Safes Made? What Kind of Gun Safe is Strongest?
Almost all the meticulous gun owners know the risks of owning some deadly weapon and the obligation and responsibility to keep it safe and secure. It is a matter of common sense to avoid any accidents, theft, r... [read more]
Check These Out
You can Get FREE Gifts. Furthermore, Free Items here. Disable Ad Blocker to receive them all.
Once done, hit anything below
 |
 |
 |
 |